Content moves rapidly, making intellectual property protection more important than ever. From videos and images to documents and audio files, creators and enterprises constantly face risks of unauthorized copying and distribution. This is where types of watermarking play a crucial role in safeguarding ownership and ensuring authenticity. By embedding identifiable marks into digital assets, organizations can track, validate, and protect content across platforms.
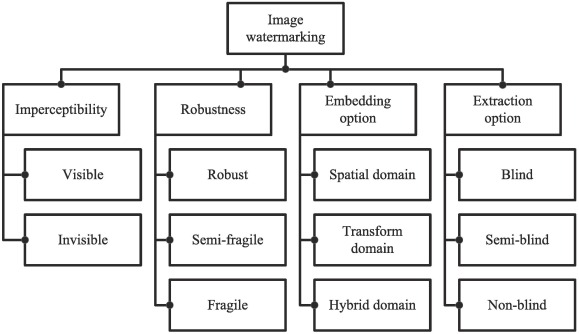
Understanding watermarking techniques helps businesses choose the right security approach based on visibility, resilience, and use case. As digital piracy rises, demand for advanced protection methods like watermarking techniques is increasing. These solutions are not one-size-fits-all and come in multiple forms designed for specific threats, helping balance user experience with strong security.
Visible Watermarking for Direct Ownership Display
Visible watermarking is the most recognizable form of content protection. It involves placing logos, text, or patterns directly on images or videos. This method clearly communicates ownership and discourages unauthorized reuse. Many photographers and media companies rely on this approach because it acts as an immediate deterrent. Among the different watermarking techniques, visible marking is best suited for promotional content where branding is essential.
However, visible marks can sometimes affect user experience, especially in high-quality media consumption. Even then, it remains one of the most widely used watermarking techniques due to its simplicity and effectiveness in asserting ownership.
Invisible Watermarking for Subtle Protection
Invisible watermarking embeds data within digital content without altering its visible appearance. This technique is highly valuable in scenarios where user experience must remain untouched. Despite being hidden, the watermark can be detected using specialized tools. This makes it a powerful solution among watermarking techniques for confidential media distribution.
Invisible marking is widely used in corporate communications, premium media content, and proprietary assets. Its strength lies in tracking unauthorized sharing while maintaining a clean visual presentation. In the broader ecosystem of watermarking techniques, this approach offers a balance between discretion and security.
Forensic Watermarking for Traceable Content Leaks
Forensic watermarking is designed to identify the source of leaks. It embeds unique identifiers into each distributed copy of content. If piracy occurs, the watermark helps trace it back to the original recipient. This makes it one of the most advanced watermarking techniques used in high-security environments such as streaming platforms and enterprise content distribution.
The strength of forensic methods lies in accountability. Since each copy is uniquely marked, it becomes extremely difficult for users to redistribute content without being identified. Among modern watermarking techniques, forensic techniques are crucial for industries dealing with high-value intellectual property.
Fragile Watermarking for Tamper Detection
Fragile watermarking is a security technique that is designed to break or get damaged whenever digital content is altered. It works like an alert system that immediately signals any modification made to the original file, ensuring that tampering cannot go unnoticed. If someone tries to edit, copy, or manipulate the content in any way, the watermark becomes corrupted or disappears entirely. This makes it one of the most sensitive types of watermarking used for strict integrity protection.
It is widely applied in legal documents, medical records, and financial data where authenticity is critical. The ability to detect even the smallest changes makes it a vital category within watermarking techniques, helping ensure that sensitive information remains original, trustworthy, and unaltered at all times.
Robust Watermarking for Long-Term Protection
Robust watermarking is built to withstand compression, resizing, cropping, and other modifications. Unlike fragile methods, it is designed to survive intentional and unintentional changes. This makes it ideal for media that is frequently shared or processed. Among watermarking techniques, robust systems are widely used in broadcasting and online media platforms.
Its resilience ensures that ownership information remains intact even when content passes through multiple systems. This durability makes robust solutions one of the most reliable watermarking techniques for long-term digital asset protection.
Digital Watermarking in Multimedia Content
Digital watermarking extends across images, audio, video, and documents. It integrates security data directly into the file structure, ensuring that protection travels with the content itself. This makes it one of the most versatile watermarking techniques in the modern digital ecosystem.
From streaming services to e-learning platforms, digital watermarking helps maintain control over content distribution. It ensures that creators retain visibility into how and where their content is used. As digital transformation expands, these watermarking techniques continue to evolve with stronger encryption and smarter embedding techniques.
Why Watermarking Matters in Digital Security
The importance of watermarking lies in its ability to combine protection with traceability. Instead of simply blocking access, it allows content owners to monitor usage and identify misuse. Across industries such as entertainment, education, and enterprise software, different watermarking techniques serve as a foundation for digital rights management strategies. These methods help ensure content authenticity while enabling tracking across multiple distribution channels.
With increasing content piracy and data leaks, watermarking is no longer optional. It is a core layer of defense that complements encryption and access control systems. Organizations adopting advanced watermarking techniques can significantly reduce revenue loss, strengthen compliance, and protect brand integrity while maintaining secure digital content distribution.
Conclusion
Digital content protection requires a layered approach, and watermarking remains one of the most effective techniques available. From visible markings to forensic tracking, each method serves a specific purpose in securing digital assets. Understanding types of watermarking allows organizations to implement the right strategy based on their content type and security needs. As threats evolve, so will the innovation behind watermarking techniques, making them a long-term necessity for content protection.
Powerful digital protection tools ensure secure content delivery worldwide effectively. Doverunner delivers advanced mobile application and content security solutions designed to protect digital ecosystems from evolving threats. Their technology secures apps, media, and streaming platforms using intelligent protection mechanisms that safeguard intellectual property and user data. With expertise in mobile app hardening, DRM integration, and anti-tampering systems, they help businesses control digital assets and reduce risks of piracy and unauthorized access.