In the shadowy depths of the dark web, where anonymity is currency and digital crimes fuel an underground economy, one platform has stood out in recent years: b1ackstash.cc. Known among cybercriminal circles b1ackstash.cc for its high-quality CVV2 data, b1ackstash.cc has carved out a reputation as a reliable source for stolen credit card information. But beyond its reputation lies a far more intricate and disturbing truth about how its CVV2 operations work—and the broader implications they have on cybersecurity, financial institutions, and everyday internet users.
In this exposé, we’ll uncover the inner workings of b1ackstash.cc’s CVV2 trade, explore how stolen data is sourced and distributed, and discuss why this illegal ecosystem continues to thrive despite increased global crackdowns.
What Is CVV2 and Why Is It Valuable?
Before diving into b1ackstash.cc specifically, it’s essential to understand what CVV2 data is and why it holds such value in underground markets.
CVV2 stands for “Card Verification Value 2”—the three-digit security code found on the back of most credit cards. When combined with other cardholder information (such as the card number, expiration date, name, and billing address), CVV2 allows fraudsters to make online purchases or conduct identity fraud without needing physical access to the card itself.
This makes CVV2 dumps—databases containing hundreds or even thousands of such entries—highly sought after in carding communities. And it’s exactly this market that b1ackstash.cc has exploited.
The Rise of b1ackstash.cc
b1ackstash.cc didn’t appear overnight. According to various intelligence reports and dark web monitoring sources, the domain began to surface around 2022, initially operating in low-profile forums and encrypted messaging apps. At first, it was regarded as “just another vendor” peddling low-tier data.
However, b1ackstash.cc soon distinguished itself by offering verified and fresh CVV2s, coupled with responsive customer support, refund policies, and even loyalty programs for repeat buyers—something almost unheard of in illegal marketplaces. Their Telegram and TOX support channels became active hives of activity, offering updates, drops, and insider-only access to premium dumps.
By mid-2023, the platform had evolved into a full-fledged carding empire.
Sourcing the Stolen Data: How Does b1ackstash.cc Operate?
One of the most pressing questions surrounding b1ackstash.cc is how they source such massive volumes of high-quality CVV2 data. While the exact methods remain opaque, several well-documented tactics have been linked to platforms like b1ackstash:
1. Phishing and Spoofing Campaigns
Sophisticated phishing kits are used to mimic bank websites, payment processors, and even email login portals. Unsuspecting users who input their credentials unknowingly hand over everything a carder needs.
2. Point-of-Sale (POS) Malware
Malicious software embedded in retail POS systems can scrape card data in real time, especially when magnetic stripe cards b1ackstash are swiped. Some of b1ackstash’s dumps have been linked to breaches in Eastern Europe and Southeast Asia.
3. Brute Force BIN Attacks
Automated tools are used to generate valid combinations of card numbers and CVV2s using known Bank Identification Numbers (BINs). These are then tested on small-value eCommerce sites before being bundled and sold.
4. Insider Breaches and Database Leaks
In certain cases, insiders at financial institutions or payment processors leak raw card data for profit. b1ackstash.cc has reportedly purchased large datasets from third-party dark web vendors with suspected insider access.
The Platform’s Business Model: Not Just a Black Market
Interestingly, b1ackstash.cc functions more like a well-organized eCommerce site than a chaotic criminal den. Here’s what their business model typically includes:
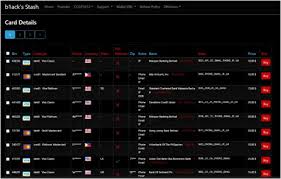
- User Accounts and Dashboards: Registered users can track orders, view inventory, and manage their balances using cryptocurrency.
- Tiered Access: Premium users gain early access to new dumps, advanced filtering tools, and exclusive payment methods.
- Search Filters: Buyers can filter cards by country, bank, card type (Visa, MasterCard, AMEX), or even cardholder ZIP code.
- Cryptocurrency Payments: Bitcoin and Monero are the standard, ensuring a semi-anonymous transaction model.
- Refund & Replacement Policy: In an effort to boost credibility, b1ackstash offers limited-time replacement for dead or invalid cards—provided certain conditions are met.
How Law Enforcement Responds—and Why It’s Not Enough
Agencies like the FBI, Europol, and Interpol have intensified efforts to dismantle operations like b1ackstash.cc. Task forces routinely monitor known forums and marketplaces, conduct undercover operations, and attempt to trace crypto wallets.
However, b1ackstash has managed to stay ahead by:
- Using bulletproof hosting in jurisdictions that don’t cooperate with international law enforcement.
- Rotating domains and access links to prevent easy takedowns.
- Employing end-to-end encryption and ephemeral communication channels (e.g., TOX, Signal, Telegram).
- Implementing customer vetting to avoid infiltration by agents or informants.
Even when specific domains are seized, backups and mirrors of the site quickly reappear, keeping the marketplace resilient.
The Human and Economic Cost
While cybercriminals rake in profits, the human and economic toll is immense:
- Victims of identity theft suffer financial loss, emotional distress, and long-term credit damage.
- Banks and merchants bear the burden of chargebacks, reimbursement, and fraud investigation costs.
- Trust in digital commerce erodes, particularly in regions frequently targeted by phishing and skimming attacks.
Estimates from cybersecurity analysts suggest that b1ackstash.cc alone may have facilitated over $20 million in fraudulent transactions in the past 12 months—a staggering number that reflects just a fragment of the total dark web fraud economy.
Conclusion: A Glimpse Into a Persistent Threat
The story of b1ackstash.cc isn’t just about one website—it’s a reflection of a larger, evolving cybercrime ecosystem that exploits weak links in digital security. As long as there is profit to be made and anonymity to be preserved, platforms like b1ackstash will continue to thrive.
The truth behind its CVV2 operations reveals a sophisticated, resilient, and dangerously effective criminal enterprise. While law enforcement is making strides, the battle is far from over.
Ultimately, cybersecurity must become a shared responsibility, not just for governments and institutions, but for individuals. Vigilance, awareness, and better digital hygiene remain our first lines of defense in a world where one mistake can end up on the dark web.